Merged
Conversation
charlesBochet
approved these changes
Nov 4, 2025
Contributor
There was a problem hiding this comment.
Greptile Overview
Greptile Summary
This PR fixes the useTriggerProviderReconnect hook by ensuring OAuth reconnection flows always redirect back to /settings/accounts after completion.
Key Changes:
- Modified the hook to always set
redirectLocationto/settings/accountsviagetSettingsPath(SettingsPath.Accounts)when callingtriggerApisOAuth - Updated all test expectations to validate that
redirectLocationis consistently set, even when custom options are provided - The change ensures a predictable user experience where reconnecting an account always returns users to the accounts settings page
Behavior:
- For OAuth providers (Google, Microsoft): Now always overrides any custom
redirectLocationin options with/settings/accounts - For IMAP_SMTP_CALDAV: Behavior unchanged - still navigates using the
useNavigateSettingshook - The spread operator
...optionsis placed beforeredirectLocation, ensuring the override always takes precedence
Confidence Score: 5/5
- This PR is safe to merge with no significant risks
- The changes are minimal, well-tested, and follow a clear intent to standardize redirect behavior. All tests have been updated to match the new behavior, demonstrating thorough coverage. The implementation correctly uses
getSettingsPathutility and properly merges options while ensuringredirectLocationis always overridden. - No files require special attention
Important Files Changed
File Analysis
| Filename | Score | Overview |
|---|---|---|
| packages/twenty-front/src/modules/settings/accounts/hooks/useTriggerProviderReconnect.ts | 4/5 | Added automatic redirectLocation override to ensure OAuth reconnections always redirect to /settings/accounts page. The change forces a consistent redirect location regardless of provided options. |
| packages/twenty-front/src/modules/settings/accounts/hooks/tests/useTriggerProviderReconnect.test.tsx | 5/5 | Updated test expectations to validate that redirectLocation is always set to /settings/accounts, even when custom options are provided. Tests comprehensively cover the new override behavior. |
Sequence Diagram
sequenceDiagram
participant User
participant Component
participant Hook as useTriggerProviderReconnect
participant OAuthHook as useTriggerApisOAuth
participant Navigate
participant Backend
User->>Component: Clicks reconnect button
Component->>Hook: triggerProviderReconnect(provider, accountId, options)
alt IMAP provider
alt no accountId provided
Hook->>Navigate: Navigate to new connection
else accountId provided
Hook->>Navigate: Navigate to edit connection
end
else OAuth provider
Note over Hook: Merge options with fixed redirectLocation
Hook->>OAuthHook: triggerApisOAuth(provider, mergedOptions)
OAuthHook->>Backend: Initiate provider flow
Backend-->>User: Redirect after completion
end
2 files reviewed, no comments
Contributor
|
🚀 Preview Environment Ready! Your preview environment is available at: http://bore.pub:34849 This environment will automatically shut down when the PR is closed or after 5 hours. |
Contributor
|
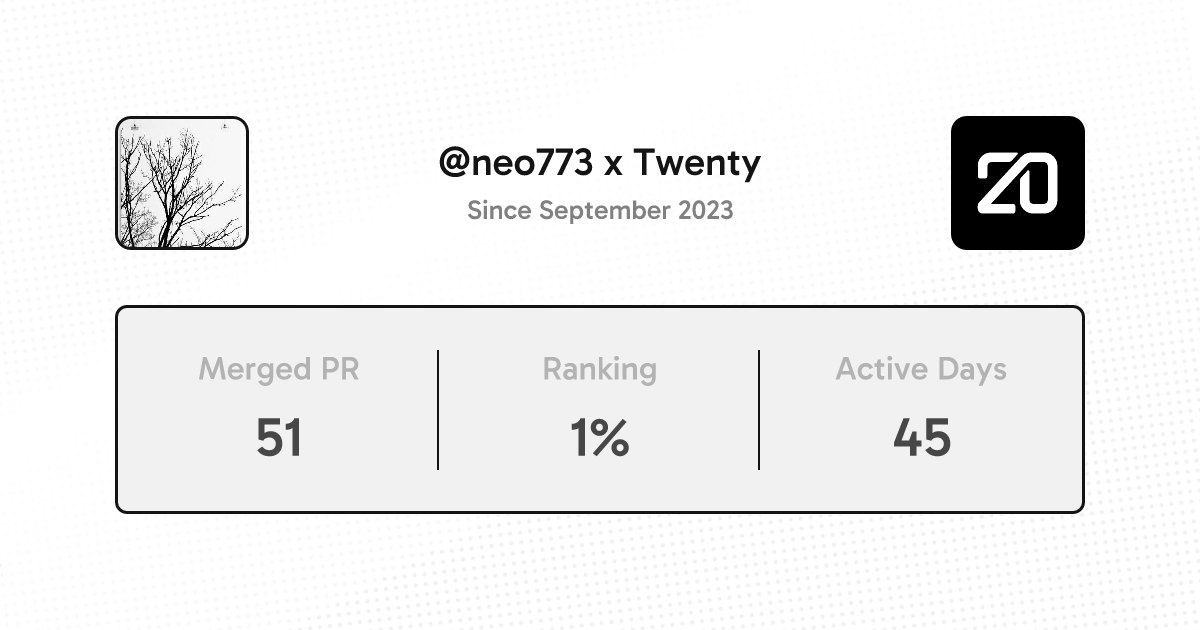
Thanks @neo773 for your contribution! |
This file contains hidden or bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
Sign up for free
to join this conversation on GitHub.
Already have an account?
Sign in to comment
Add this suggestion to a batch that can be applied as a single commit.This suggestion is invalid because no changes were made to the code.Suggestions cannot be applied while the pull request is closed.Suggestions cannot be applied while viewing a subset of changes.Only one suggestion per line can be applied in a batch.Add this suggestion to a batch that can be applied as a single commit.Applying suggestions on deleted lines is not supported.You must change the existing code in this line in order to create a valid suggestion.Outdated suggestions cannot be applied.This suggestion has been applied or marked resolved.Suggestions cannot be applied from pending reviews.Suggestions cannot be applied on multi-line comments.Suggestions cannot be applied while the pull request is queued to merge.Suggestion cannot be applied right now. Please check back later.
No description provided.